Russia is believed to have hacked US satellite communications provider Viasat on the day of its invasion of Ukraine.
Western intelligence agencies have been investigating the incident and while they have not yet made a public accusation, they believe Russia was behind it.
It appears to be the most significant cyber-attack linked to the conflict so far, affecting military, as well as government, communications.

Overall though, Western officials say Ukraine has proved more resilient to cyber-attacks than many had expected.
Western intelligence agencies are investigating the hacking of Viasat, which provides communications through a network of satellites.
It appears to have been hit by a sophisticated cyber-attack that wiped devices on the day the invasion began.

It also affected other countries in Europe, although not the UK.
Viasat told the BBC that it was replacing some customers’ modems but its core network infrastructure and the satellite itself were not damaged.
“Viasat is actively working with distributors to restore service for those fixed broadband users in Europe impacted by this event,” it said in a statement.
The company did not say who it thought was behind the cyber-attack and said the US government would provide attribution in due course.
Military doctrine
“It looks like the clearest example of spill-over,” said one official.
Western officials believe this was almost certainly the work of Russia but have not yet assembled the evidence to make a public accusation.
“Were it to be ultimately attributed to Russia, it would very much fit with what we expect them to do, which is use their cyber-capability to support their military campaign,” said one Western official.
They believe it fits closely into Russian military doctrine, in which cyber-attacks are used to support specific military objectives – in this case trying to sow confusion by disrupting Ukrainian command and control.
In recent days, US cyber-authorities have warned that they are “aware of possible threats to US and international satellite communication networks”, and America’s FBI and Cybersecurity and Infrastructure Security Agency (Cisa) have urged providers to improve their security because of the continuing potential risks.
Russia’s military intelligence agency, the GRU, is thought to have been behind the Viasat hack, according to a report in the Washington Post.
Other officials also say that the GRU has led in operations against Ukraine.
Limited tech damage
In the initial phases of the Russian invasion, many had predicted large-scale destructive cyber-activity from Moscow.
Russian state hackers linked to the GRU in the past have managed to turn off the power for hundreds of thousands of Ukrainians. But nothing on this scale was seen.
Western analysts believe there are several reasons for the absence of significant destructive attacks.
Russia believed the government in Kyiv would be toppled quickly and a new pro-Moscow replacement would be put in place.
In this scenario, destroying infrastructure would serve little purpose.
Destructive cyber-attacks take time to prepare and Moscow’s state hackers may also not have had sufficient notice since, like much of the military, they may not have known an invasion was being planned until the last minute.
Another reason is that when it comes to a full military conflict, hard military power can be more reliable in destroying targets such as TV towers than cyber-attacks, which are not always guaranteed to work.
But Western officials caution against the idea that there have not been cyber-attacks. They say that the Ukrainians may simply have been resilient to the attacks that did come their way.
Ukraine resilience
“We have seen broad targeting of Ukrainian networks and systems,” one official said.
“There was a significant amount of intent on the part of Russia to disrupt Ukrainian systems before the invasion,” an official also noted.
So-called “wiper” software was used to target government systems in January and February, just days before the invasion.
But officials say they believe Ukrainian defences held up well against attacks, which came from several Russian state-linked groups.
The experience of previous attacks may also have helped.
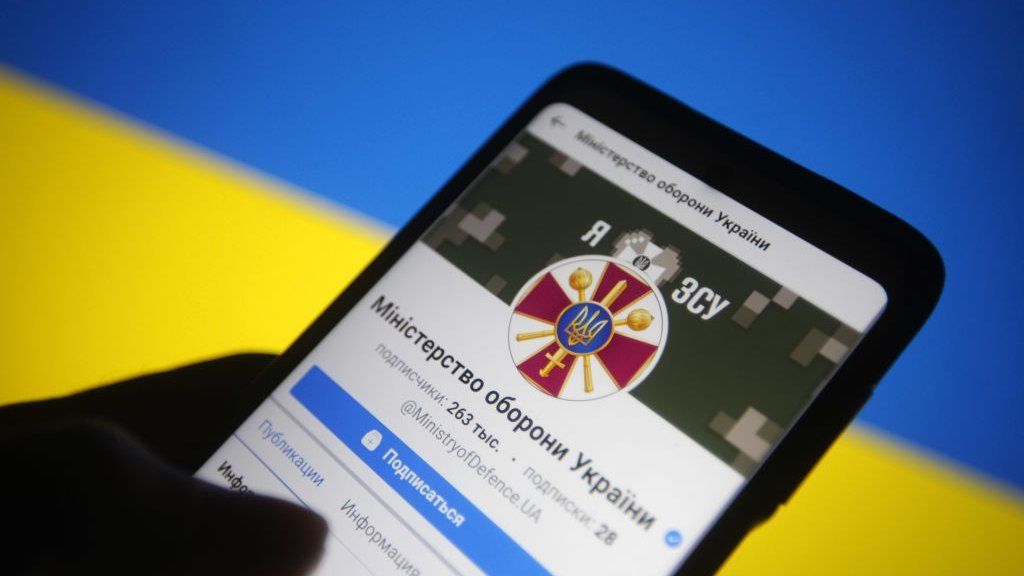 IMAGE SOURCE,GETTY IMAGES
IMAGE SOURCE,GETTY IMAGES“The Russians perhaps helped the Ukrainians get match fit,” an official said.
“Ukraine has done an incredible job of being resilient,” said the official, adding that the country had received extensive support from the West, in terms of both government and private sector.
Both US and UK cyber-intelligence officials have been working closely for a long period with Ukrainian counterparts, including in specific areas such as telecoms.
“That’s an area that they put a significant amount of effort into, and was supported by allies,” officials said.
There has been continued cyber-espionage in the conflict by both sides, officials say, particularly around intercepting communications and trying to locate and target individuals and military formations.
‘Possible activity’
So far, there have also not been major cyber-attacks against the West from Moscow.
One concern had been that Russia could retaliate for Western sanctions by launching cyber-attacks against the West, perhaps unleashing criminal gangs who use ransomware to lock businesses and organisations out of their systems.
The White House did warn this week that it has seen intelligence of possible activity.
However, it is not clear yet whether this is above the normal level of Russian cyber-activity that is happening all the time or whether it is an indication that Russia is preparing for something more serious.
On Thursday, the US Department of Justice and UK Foreign Office also accused Russia’s Security Service, the FSB, of hacking into energy providers between 2012 and 2018.
Source: bbc news
Other stories
-
EU signs US gas deal to curb reliance on Russia
-
Russia considers tolerating Bitcoin for oil and gas
-
Is type 1 diabetes a handicap, and would you be able to guarantee benefits for it?
-
How to Get Backlinks (15 Quick and Simple Strategies)
-
Instructions to apply for educational loan in Ghana
CLICK ON THE LINK TO FOLLOW US ON FACEBOOK
CLICK ON THE LINK TO FOLLOW US ON TWITTER